Why I joined Sysdig
When choosing your next role, they say to look for alignment in values. For me, that's always been about innovation, transparency, and making a real impact in security. In Sysdig, I found all three.
My mission: Leading cybersecurity, protecting both Sysdig and our customers, while helping organizations worldwide defend against cloud threats at speed. We're building cloud-native security that moves at an engineering pace, powered by open source, driven by innovation, and loved by customers. The best part? Sysdig's amazing engineering team isn't just building products - they're strengthening the entire security ecosystem.
But what truly sold me? Two aspects:
1. Open Source Warriors: From Wireshark to Falco, the global foundation for cloud threat detection
Loris Degioanni, the founder of Sysdig, not only gifted together with Gerald Combs Wireshark to the world but also created Falco, the most adopted open-source runtime & observability security solution out there and the rules engine upon which Sysdig is built.
If security products are the immune system of the digital world, open source is its DNA — constantly evolving, adapting, and sharing improvements across the entire ecosystem. Take Snort/Suricata/Zeek, Nmap, qemu, ELK, ModSecurity, OPA, Sigstore, Yara, Sigma, bindiff, semgrep and many other projects and formats which secured countless companies and inspired so many cyberfounders and innovators to build upon them. This collaborative spirit continues to strengthen our digital immune system, as developers, security teams, and innovators worldwide contribute to building a more resilient and transparent security ecosystem for all.
Falco's recent CNCF graduation stands as a testament to the power of transparency and open source collaboration for securing our digital future. You can discover Falco's journey and capabilities and start contributing through the wealth of KubeCon presentations, where the community shares its vision for cloud-native security.
2. Isn’t the Industry Shifting Left, Why Focus on Runtime Security at all?
As security leaders, we face a growing challenge: keeping pace with rapidly evolving software and AI innovations and avoiding blocking the developers working on it. This paradigm shift isn't just a temporary hurdle – we're at a critical inflection point where multiple market forces are converging, indicating the time is ripe for Sysdig’s runtime-centric cloud security:
2.1 Runtime security is our first line of defense. Period.
First of all, we need to talk about signal-to-noise in vulnerability management: On average, more than 85% of vulnerabilities identified by security controls are not exploitable. If you want to know with certainty which vulnerable libraries and functions are used (reachability), runtime insights provide the most precise feedback vs. theoretical code paths of code analysis.
If you have to pick one single security control in your cloud, you will never go for code scanners or agentless workload protection unless you follow the marketing buzz of some vendors. Like in the on-prem world, EDR is your #1 control; for your cloud and containers, runtime security is #1.
If everything else fails, runtime security is the only way to detect and stop attacks or lateral movement. Considering more than 96% of modern software is built with third-party open source code, you must plan for the next wave of Log4J vulnerabilities or XZ backdoors. In the same way there is a clear expert consent the output of GenAI Agents cannot be trusted. Assume your production has vulnerabilities. Assume supply chain backdoors. Assume lateral movement in the cloud. Assume breaches.
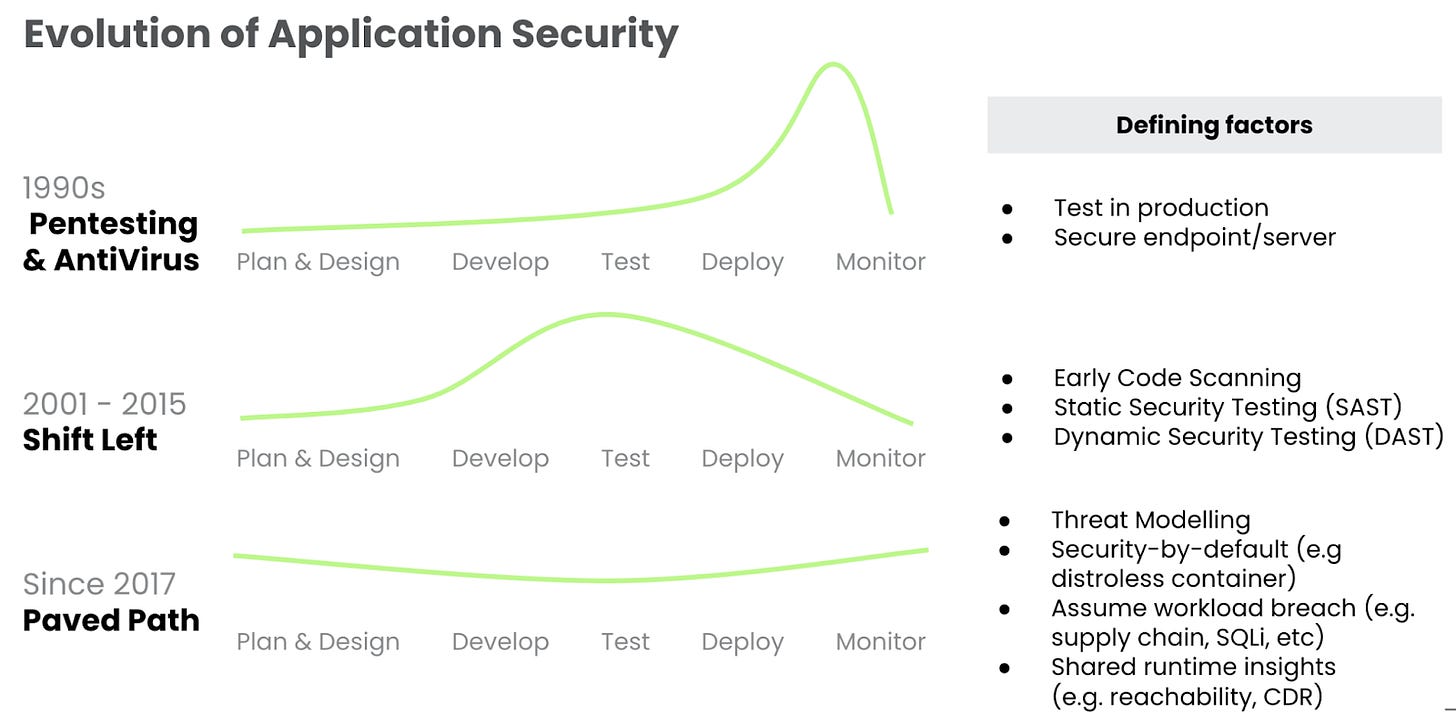
2.2 Shift left was perfect for old IT, but the cloud plays by new rules.
Twenty years ago, when the concept of Shift Left was introduced for the first time, software was shipped on a CD-ROM (it feels like I am getting old!), and working for a bank sometimes took us up to 40 weeks to update a banking application. Yes, it made sense to double down on making everything possible to detect defects earlier and avoid risks and especially high costs of changing software!
Today, modern architecture and continuous CI/CD software are updated every 24 hours. The tons of code scanners producing false-positive noise and blocking your business do not simply account for the benefit. Security has to be balanced out throughout the entire lifecycle and not just pushed to the “left.”
Modern product security programs focus instead on paved roads (secure container images such as Chainguard, more threat modeling) and mitigating the small number of potential defects with runtime security, instead of blocking pipelines due to tons of false positives from code scanners during build.
Ask yourself: What's the best way to move at the speed of your software engineers?
2.3 The complexity of the cloud and the speed of attacks mandates real-time detection, forensics, and response capabilities.
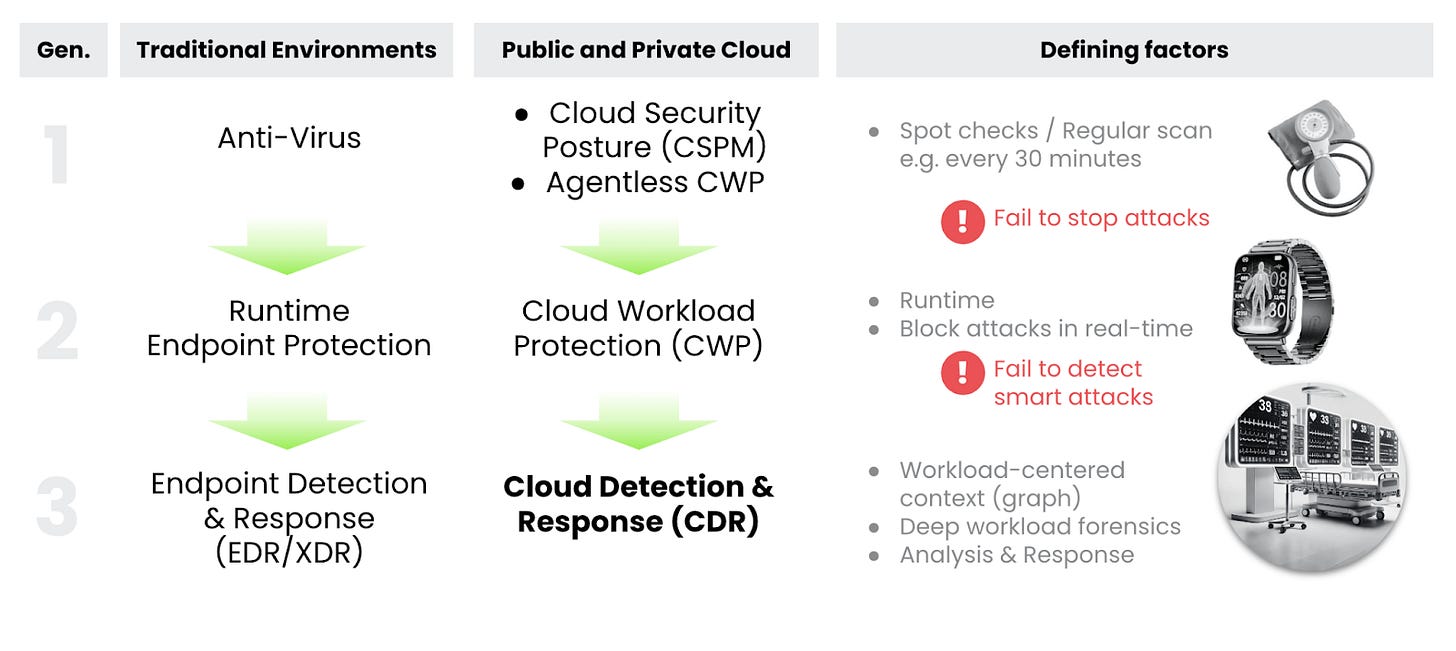
Relying only on security posture management (e.g. CSPM) is like protecting your factory with locked doors and the occasional guard patrols instead of 24/7 video surveillance. Just as modern physical security needs constant monitoring, cloud security demands real-time detection and response.
It's not an easy challenge: Cloud attacks move at lightning speed — just 10 minutes from start to finish. Compare that to traditional on-premises attacks that take 8-14 hours. The math is simple: we need capabilities to detect, analyze, and respond within minutes.
Traditional EDR tools were built for the on-prem environment. But the cloud is different — workloads appear and disappear in minutes, and containers spin up and down constantly. Just as security teams pushed antivirus to evolve into EDR, they're now demanding cloud security platforms that can match this dynamic environment.
It’s primetime for runtime
I’m excited to join Sysdig, and I’m ready to roll up my sleeves and help write the next chapter in runtime-centered cloud security. It’s primetime for runtime! Let's connect if you're passionate about open source, cloud and container security, or just want to chat about what's next in our industry!